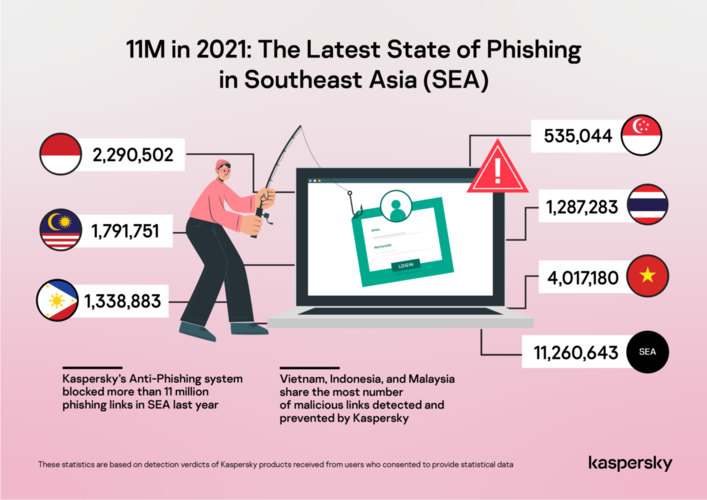
Kaspersky’s anti-phishing system blocked a total of 11,260,643 phishing links in Southeast Asia in 2021, with most of it blocked on devices of Kaspersky users in Vietnam, Indonesia and Malaysia.
Kaspersky’s data revealed that by including hot topics and phrases related to their online activities like shopping and streaming entertainment or the Covid-19 pandemic in their messages, the chances of an unsuspected user clicking infected links or malicious attachments increase tremendously.
Kaspersky Southeast Asia general manager Yeo Siang Tiong said email is the main mode of communication for work in Southeast Asia and 11 million phishing attempts in one year is just the tip of the iceberg.
“With all the critical data being sent via email, it is expected for cybercriminals to see it as an effective and lucrative entry point. An unfortunate example is the $81M Bangladesh Bank heist in 2016 which was made possible by a single, successful targeted phishing attack.
“Enterprises in the region should carefully look into holistic and in-depth cybersecurity technologies to beef up the security of their highly critical mail servers,” he said.
Kaspersky said the remote work triggered more attempts to phish corporate details for the past two years. Among the rising trends is business email compromise (BEC).
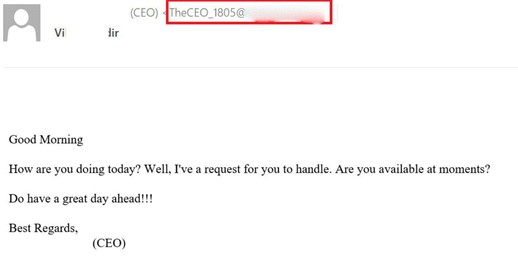
BEC attacks are a type of fraud that involves impersonating a representative from a trusted business. A BEC attack is defined as a targeted cybercriminal campaign that works by:
- Initiating an e-mail exchange with a company employee, or taking over an existing one
- Gaining the employee’s trust
- Encouraging actions that are detrimental to the interests of the company or its clients
According to US wireless network operator Verizon, BEC was the second most common type of social engineering attack in 2021, and the FBI reported that BEC attacks cost U.S. businesses over $2 billion from 2014 to 2019.
Kaspersky experts are increasingly observing BEC attacks. In Q4 2021, Kaspersky products prevented over 8000 BEC attacks, with the greatest number (5,037) occurring in October.
Throughout 2021, the company’s researchers found out that the attacks tend to fall into two categories: large-scale and highly targeted.
The large-scale attack is called “BEC-as-a-Service”, where attackers sent streamlined messages en masse from free mail accounts, with the hope of snaring as many victims as possible. Such messages often lack high levels of sophistication, but they are efficient.
The more advanced targeted BEC attacks works as follows: attackers first attack an intermediary mailbox, gaining access to that account’s e-mail. Then, once they find a suitable correspondence in the compromised mailbox of the intermediary company, they continue the correspondence with the targeted company, impersonating the intermediary company. Often the goal is to persuade the victim to transfer money or install malware.
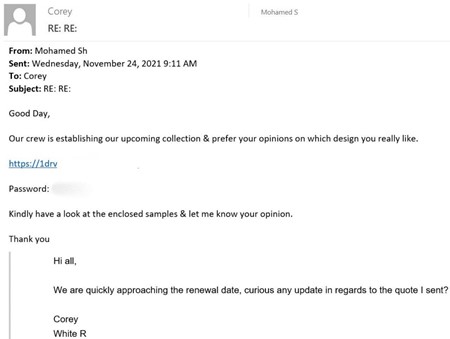
Kaspersky security expert Roman Dedenok said BEC attacks have become one of the most spread social engineering techniques.
“The reason for that is pretty simple – scammers use such schemes because they work. While fewer people tend to fall for simple mass-scale fake emails now, fraudsters started to carefully harvest data about their victims and then use it to build trust. Some of these attacks are possible because cybercriminals can easily find names and job positions of employees as well as lists of contacts in open access. That is why we encourage users to be careful at work,” he said.
Cybercriminals use various technical tricks and social-engineering methods to win trust and carry out fraud. However, enterprises can take effective measures to minimize the threat from BEC attacks:
- Set up Sender Policy Framework (SPF), use DomainKeys Identified Mail (DKIM) signatures, and implement a Domain-Based Message Authentication, Reporting & Conformance (DMARC) policy to guard against fake internal correspondence.
In theory, these measures also permit other companies to authenticate e-mails sent in the name of the organizations. This method falls short in some ways, such as not being able to prevent ghost spoofing or lookalike domains. But if more companies use SPF, DKIM, and DMARC, there will be less wiggle room for cybercriminals. Use of these technologies contributes to a kind of collective immunity against many types of malicious operations with e-mail headers.
- Train employees periodically to counter social engineering. A combination of workshops and simulations trains employees to be vigilant and identify BEC attacks that get through other layers of defense.
- Use security tools to protect corporate communication channels such as Kaspersky Secure Mail Gateway email security solution with the set of anti-phishing, anti-spam, malware detection technologies.
- Subscribe to an in-depth and regularly updated threat intelligence services (IT service) to have an in-depth visibility into cyberthreats targeting organizations.







