
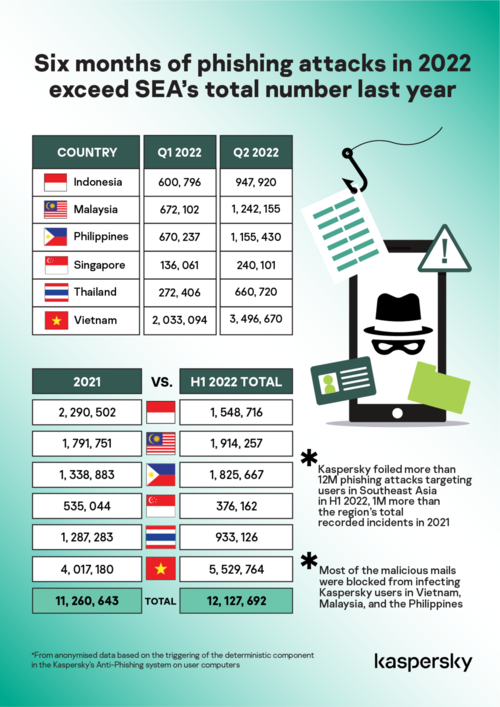
Phishing incidents continue to skyrocket in Southeast Asia (SEA) with phishing attacks in the first six months of 2022 exceed the total number in 2021.
The latest data from global cybersecurity company Kaspersky revealed that it only took six months for cybercriminals to exceed their phishing attacks last year against users from the region.
More than half of the first half of 2022 detections were targeting Kaspersky users in Malaysia, the Philippines and Vietnam.
Four out of six countries from SEA – Malaysia, the Philippines, Thailand, and Vietnam – recorded more phishing emails during the first six months of this year compared to their total number of incidents in 2021.
From January to June 2022, Kaspersky’s anti-phishing system blocked a total of 12,127,692 malicious links in SEA, which is one million more than the 11,260,643 phishing attacks detected in the region in 2021.
Phishing, a type of social engineering attack, remains one of the key methods used by attackers to compromise their targets, both individuals and organizations.
It is done on a large scale where cybercriminals send massive waves of emails purporting to be legitimate companies or personalities to promote fake pages (phishing sites) or infect users with malicious attachments.
The end goal of a phishing attack is to steal credentials, particularly financial and login information, to steal money or worst to compromise an entire organization.
“The first half of 2022 is eventful in good and bad ways. On a personal level, we went through the seismic shift of trying to regain our lives post-pandemic, forcing companies and organizations to welcome remote and hybrid work.
“The travel sector, including airlines, airports and travel agencies, has also been overwhelmed by the influx of tourists wanting to travel with borders now open,” said Kaspersky Southeast Asia general manager Yeo Siang Tiong.
He continued, “Behind these shifts are networks and systems that needed to be updated and secured hastily. On the other hand, cybercriminals are all ears and with their ability to tweak their messages and infuse them with believable urgency.”
“As a result, we’ve seen real, unfortunate incidents of victims losing money because of phishing attacks,” Yeo added.
Aside from individual’s loss of money, Kaspersky’s researcher recently sounded the alarm that most of the Advanced Persistent Threat (APT) groups in the Asia Pacific including SEA use targeted phishing to enter into a highly-defended network.
As the name “advanced” suggests, an APT uses continuous, clandestine, and sophisticated hacking techniques to gain access to a system and remain inside for a prolonged period of time, with potentially destructive consequences.
APTs are usually leveled at high-value targets, such as nation states and large corporations, with the ultimate goal of stealing information over a long period of time, rather than simply “dipping in” and leaving quickly, as many black hat hackers do during lower level cyber assaults.
Noushin Shabab, senior security researcher for Global Research and Analysis Team (GReAT) at Kaspersky, revealed in a recent presentation that targeted phishing, also known as spear phishing, is the preferred infection vector of APT groups operating in the region.
Yeo said Kaspersky recently found that majority (75%) of executives in the region are aware and even anticipate an APT attack against their organizations.
“With phishing incidents hitting the roof in just the first six months of the year, enterprises, public entities and government agencies should understand the impact of one wrong click on their critical networks and systems.”
Yeo said backup security plans like incident response capabilities should be in place to stop a phishing email from becoming the launch pad of a damaging attack to an organization.
“Traditional security often doesn’t stop spear phishing attacks because they are so cleverly customized. As a result, they’re becoming more difficult to detect. One employee mistake can have serious consequences for businesses, governments and even nonprofit organizations,” he added.
With stolen data, fraudsters can reveal commercially sensitive information, manipulate stock prices or commit various acts of espionage.
In addition, spear phishing attacks can deploy malware to hijack computers, organizing them into enormous networks called botnets that can be used for denial of service attacks.
To fight spear phishing scams, employees need to be aware of threats, such as bogus emails landing in their inbox. Besides education, technology that focuses on email security is necessary.
Kaspersky recommends installing protective anti-phishing solutions on mail servers as well as on employee workstations.
As for enterprises and organizations, Kaspersky suggests building incident response capabilities that will help manage the aftermath of an attack and to incorporate threat intelligence services to have in-depth knowledge of evolving threat and tactics of active APT groups.







